Solutions
Payment
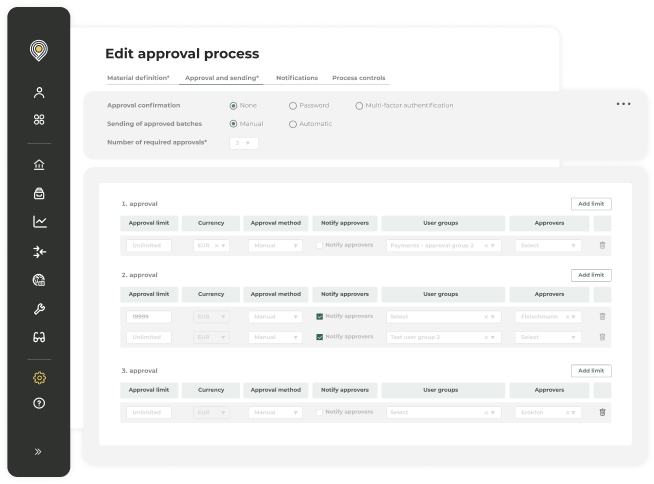
process controls
Built-in payment process controls for fraud prevention, compliance with treasury and finance policies, and data validation.
-1.png?width=572&height=525&name=hero%20(1)-1.png)
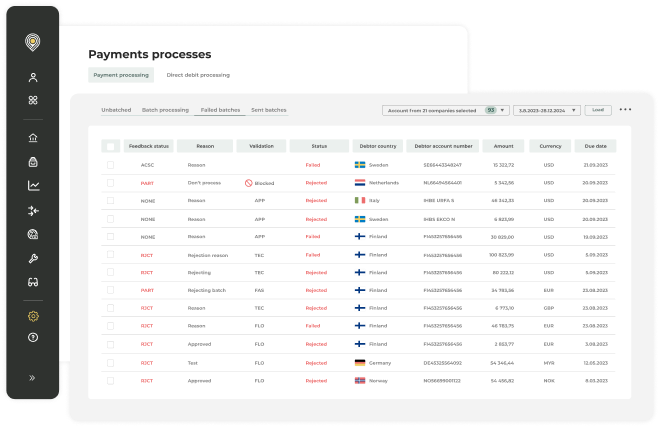
Automatically detect anomalies in outgoing payments
Tackle fraud and errors and improve payment process’ compliance & security.
Prevent fraud and errors
Set up rules to automatically detect payment anomalies and prevent double payments.
Enforce treasury & finance policies
Enforce rules based on company-wide treasury and finance policies to detect and prevent irregularities.
Ensure data reliability
Ensure payment data quality with automatic validation checks and algorithms. Get alerted when data is invalid.
Additional security. Now embedded into all your payment processes.
Fraud prevention for outgoing payments
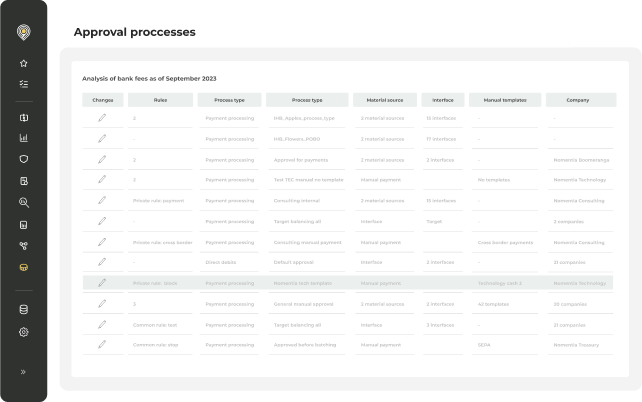
Prevent payment fraud and catch anomalies by setting up smart rules to screen all outgoing payments.
- Create rules to prevent both internal and external fraud
- Set up rules that can help detecting anomalies in outgoing payments
- Get notified when the system catches any anomalies and stop the outgoing payments from being processed
- Review all escalated outgoing payments before sending the payment to the bank
- Create rules to prevent accidental double payments
Ensure compliance with treasury
& finance policies
Make sure that all payment transactions are executed accurately, securely, and in accordance with your policies.
- Define and create rules based on your internal policies
- Enforce payment process policies to improve transaction accuracy
- Detect payment process irregularities and get notified about any deviation
Make sure payment data is correct with
automatic data validation rules
Maintain payments data quality using data validation checks and algorithms.
- The solution comes with built-in data validation to ensure data quality. For example, you can validate payments based on IBAN, names, countries, and more.
- Get alerted when the system catches any invalid or missing data.
- Define what actions should happen when certain conditions are met.
- The functionality is always included in our payments solution.
Trusted by 1400+ customers worldwide
Katriina Järvenpää
Financial Development, Senior Manager, Posti Group
Katriina Järvenpää
Financial Development, Senior Manager, Posti Group














Integrate with the tools
you rely on every day
Nomentia integrates with the banks, systems and tools you use everyday.
Find out more
Want to know more about our payment
process controls module?
Let's discuss the future of your treasury processes together.